AT&T inspired me to explore a little more.

After my encounter with proactive SMS from an AT&T SIM, I decided to start checking other SIMs as well. I know nearly all SIMs support proactive features, but I am interested to see just how many SIMs actually use them. So I have set up my test bench to test the SIMs I have.
The SIMs
In this first round, I am limiting my testing to SIMs from the big “tier-1” operators, SIMs that are use by large numbers of people. Here is what I have on-hand:
- AT&T (already covered but listed here for completeness)
- Verizon
- T-Mobile USA
- Vodafone Romania
- Orange Romania
All of these SIMs were issued between 2014 and 2019.
The Test Bench
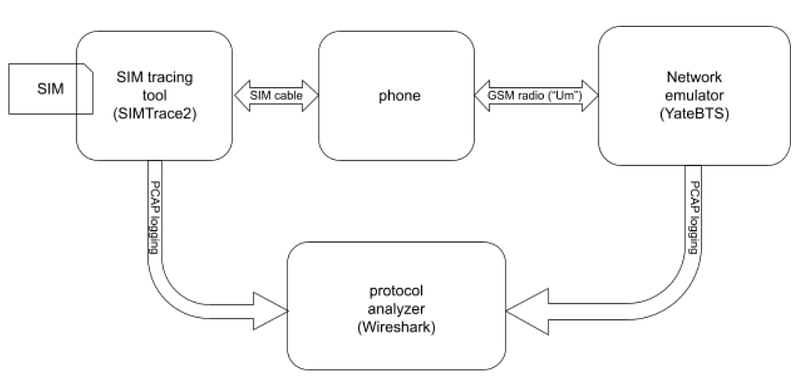
The test bench is the same as in the first article, repeated here for convenience:
- The SIMTrace2 tool, which sits between the SIM and the phone, allowing us to sniff the communication between them.
- A host phone. I used an Allview Soul.
- The Legba Lab Kit, desktop network emulator.
- A generic smart card reader and the PySim SIM management software.
The Procedure
The purpose of the procedure is to monitor the communication between the SIM and the phone to see what proactive features the SIM is using. To get the SIM to be active, we will use the Lab Kit to mimic the SIM’s home network. Here are the steps:
- The “SUT” is the “SIM Under Test”.
- Use PySim and the card reader to get the SUT’s IMSI.
- Use the first 5 or 6 digits of the IMSI to get the home network PLMN of the SUT.
- Program the SUT’s home network PLMN into the Lab Kit’s GSM cell emulator.
- Turn off the phone.
- Install the SUT into the SIMTrace2 device.
- Start a fresh capture in Wireshark.
- Start the simtrace2-sniff program, with packets directed to your Wireshark host.
- Power up the phone.
- Usually, the phone will recognize its SIM’s home PLMN and attach to the emulated network immediately. If not, select it manually.
- Just let the phone sit for at least 5 minutes.
- Make a short phone call.
- Send an SMS to yourself.
- Let the phone sit for another 5 minutes.
- Check the Wireshark log for proactive operations.
For SIMs that are still valid and have coverage, the emulator is not required, and you can skip Step #4.
The Results
So, just to get it out of the way, here are the uninteresting ones tested so far:
- Vodafone Romania
All the others were interesting.
All of the SIMs used a proactive supplementary services operation to change the call forwarding, but that does not count as “interesting”. I left an example here in Pastebin just in case anyone disagrees.
Now for the more interesting ones.
AT&T
AT&T had a whole post to itself, but is summarized here for convenience. The AT&T SIMs that I have tested send an SMS to AT&T whenever they detect a change in the IMEISV. This IMEISV change is triggered by a baseband processor firmware update, or by moving the SIM to another phone. This type of SIM is covered in detail in the earlier article.
Verizon
The Verizon SIMs that I tested attempt to open TCP/TP sessions on port 8443 at several IP addresses in the 63.55.x.x and 69.78.x.x blocks, using an APN called “vznadmin”. Since this is a special APN, it is not clear if these IP addresses are really public in this context, but if these IP addresses are public, WHOIS shows that they are owned by Verizon. Since none of these servers responded, I never got to see what the SIM was really trying, but I did see the TCP/IP SYN packets in the SNDCP layer of the Lab Kit, so, yes, the baseband processor really was trying to open these sessions. (Oh, you didn’t know that SIMs could open data sessions that are completely invisible to the application processor?) I saved an example of one of these SIM messages here on Pastebin.
T-Mobile USA
This SIM sometimes uses proactive SMS to send a UDP packet to port 1808 on some server at ISDN address 122 . It is sent through T-Mobile USA’s standard SMSC at +12063130004. The payload is binary-encoded and contains ASCII text: “Activate:dt=15”. (Normal text encoding for SMS uses the GSM 7-bit character set, not ASCII. This is an M2M message.) An example of the MO-SMS, taken from the network side, is available here on Pastebin.
Orange Romania
This SIM tries to send a binary payload SMS to ISDN address 5692 through Orange Romania’s standard SMSC at +40744946000. There is a full example saved here on Pastebin What’s the content?
Straight outta Wireshark, we have:
- 0060 XX XX XX 11 51 01 01 03 08 3a 25 76 03 08 91 23 ..;.Q….:%v…#
- 0070 06 04 0a 98 04 01 81 10 11 30 73 48 f5 05 09 08 ………0sH….
- 0080 29 62 01 62 20 51 23 61 06 14 ff ff ff ff bf 4f )b.b Q#a…….O
- 0090 80 ef 7f 00 80 0f 71 84 08 83 63 60 00 00 90 00 ……q…c`….
Like the AT&T 2015 example, this message uses TLV formatting and most of the fields are obvious:
- 11 51 01: Header
- 03 08 3a 25 76 03 08 91 23 06 : field type 0x03, length 0x08, IMEI
- 04 0a 98 04 01 81 10 11 30 73 48 f5 : field type 0x04, length 0x0a, ICCID
- 05 09 08 29 62 01 62 20 51 23 61 : field type 0x05, length 0x09, IMSI
- 06 14 ff ff ff ff bf 4f 80 ef 7f 00 80 0f 71 84 08 83 63 60 00 00 : field type 0x06, length 0x14, probably a terminal profile
- 90 00: field type 0x09, length 0, unknown
Conclusion
Of the five tier-1 SIMs I just have “laying around”, four of them proactively send messages or initiate connections through the cellular modem. Since these operations are happening between the SIM and the baseband processor, they are probably completely undetectable from the application processor and its Android/iOS/whatever software.
I hope this is the start of a much larger exploration of proactive SIMs from around the world.